Please fill out the fields below so we can help you better. Note: you must provide your domain name to get help. Domain names for issued certificates are all made public in Certificate Transparency logs (e.g. crt.sh | example.com), so withholding your domain name here does not increase secrecy, but only makes it harder for us to provide help.
My domain is:
http://portal.applebywestward.co.uk/
I ran this command:
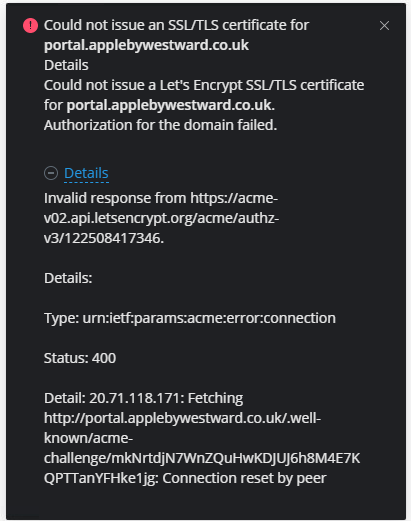
Auto-renew and manual reissue fails
It produced this output:
My web server is (include version):
CPU Intel(R) Xeon(R) Platinum 8272CL CPU @ 2.60GHz (2 core(s))
Version Plesk Obsidian v18.0.44_build1800220614.18 os_Ubuntu 20.04
OS Ubuntu 20.04.4 LTS
System Uptime: 203 day(s) 22:30
The operating system my web server runs on is (include version):
As above screenshot: Ubuntu 20.04.4 LTS
My hosting provider, if applicable, is:
Inside an Azure secure network managed by the parent company.
I can login to a root shell on my machine (yes or no, or I don't know):
Yes, from within a Citrix secure network
I'm using a control panel to manage my site (no, or provide the name and version of the control panel):
Plesk: PLSK.08021520.0011
The version of my client is (e.g. output of certbot --version or certbot-auto --version if you're using Certbot):
I'm not sure what this is?
Additional notes:
We have had firewall issues in the past since these are controlled by the parent company. Perhaps this is an issue still?
When the challenge file is created, I can access from within a browser, however, from within Plesk the reissue and auto-renew fails.
The website and certificate were working fine until certificate auto-renew (in Plesk) was attempted.
Any help will be gratefully received.