Hi friends,
I am activating proftpd service with encrypted connection.
For to do so, I’ve created the file /etc/proftpd/conf.d/sftp.conf:
<IfModule mod_dso.c>
# If mod_tls was built as a shared/DSO module, load it
LoadModule mod_tls.c
</IfModule>
<IfModule mod_tls.c>
TLSEngine on
Port 2222
TLSLog /var/log/proftpd/sftp.log
# Support both SSLv3 and TLSv1
TLSProtocol SSLv3 TLSv1
# Configure both the RSA and DSA host keys, using the same host key
# files that OpenSSH uses.
TLSEngine on
TLSRSACertificateFile /etc/letsencrypt/live/server.sio4.org/cert.pem
TLSRSACertificateKeyFile /etc/letsencrypt/live/server.sio4.org/privkey.pem
TLSCACertificateFile /etc/letsencrypt/live/server.sio4.org/chain.pem
# Authenticate clients that want to use FTP over TLS?
TLSVerifyClient off
# Allow SSL/TLS renegotiations when the client requests them, but
# do not force the renegotations. Some clients do not support
# SSL/TLS renegotiations; when mod_tls forces a renegotiation, these
# clients will close the data connection, or there will be a timeout
# on an idle data connection.
TLSRenegotiate none
# Enable compression
SFTPCompression delayed
</IfModule>
Following these guidelines: http://www.proftpd.org/docs/howto/TLS.html
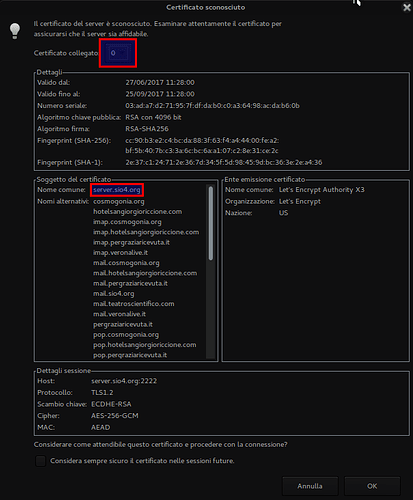
Now if I try to connect to server.sio4.org with username and password, from (for example) ftp client Filezilla it asks me to recognize two certificate:
Where I’m wrong?
Many thanks!