Why would you post the private key?
You will now have to revoke it and get a new one.
NEVER NEVER NEVER share/post/show the private key to anyone anywhere.
Sorry, I didn't think about it .. it stayed online for a few minutes .. I just took it off
I also took it off but it can still be seen and will be seen by crawlers via the orange edit pencil link.
![]()
You now need to revoke it and get a new one.
@rg305 I have already hidden the revision
It was a stupid mistake, I apologize for the confusion I caused. @rg305 since @sahsanu immediately hid it, do I still have to revoke it, or can we move on?
@vettalex you should revoke it anyway: hidden still means moderators or above still can see
@sahsanu as this runs with LE staffs (and mod saw it) would this trigger CA/B BR 4.9.1.1?
The CA SHALL revoke a Certificate within 24 hours if one or more of the following occurs
...
3. The CA obtains evidence that the Subscriber’s Private Key corresponding to the
Public Key in the Certificate suffered a Key Compromise
certificate in question is crt.sh | 5337757897 if key posted is for cert.pem he posted too.
Ok guys, so I have to revoke it.
Currently this certificate is dedicated to the zimbra server where all the customer mailboxes are configured. Will they have any disruption by revoking the certificate?
I am reading the faq to carry out the revocation:
Can you give me some advice on which command I should use?
Last year I created the certificate through Certbot
@orangepizza Thank you. I agree, the private key has been compromised and it shall be revoked.
@lestaff @vettalex posted an image with the full content of the private key. We have hidden it but anyway, the key has been compromised. Could you please take care? Thank you in advance.
@vettalex it doesn't matter whether it was just a few minutes showing the image with your private key, you must create a new one and get new certs.
Cheers,
sahsanu
Yes, I agree, I look forward to @lestaff . Sorry again
expect revoked certificate cause wreck havoc unless replaced (not sure how many mail server actually check ocsp though):
you can revoke old certificate private key with
certbot revoke --cert-path /PATH/TO/cert.pem --key-path /PATH/TO/key.pem --reason keycompromise
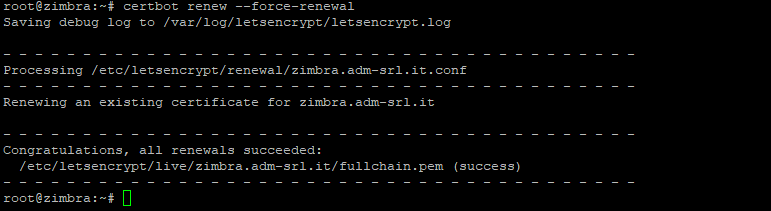
then use certbot renew --force-renewal for this time(and this time only, don't put that on cron) . as timer didn't run out but you'll have to run the renewal process.
Ok, after the revoke command ... after how long do I renew?
right after. I think you could do that in two line script if you want
you should put your certificate's path to revoke. you left /PATH/TO/cert.pem and /PATH/TO/key.pem as is
but looks like LE staff is come to revoke the certificate so maybe skip the revoke and just force renew the certificate and let staff to the revocation for you 
Thanks for pointing out the key compromise! The best way to notify us formally about a key compromise is either (a) revoke via the API or (b) email cert-prob-reports@ (listed in our CPS). Since this was presumably posted as a screenshot I'm guessing it would be a big hassle to transcribe it, so I'll send this along to cert-prob-reports@. We have a ticketing system there and tracking to make sure nothing lingers past the deadline.
Ok, so I'm waiting for LE? or can I already do a renew?
you can renew the certificate already with --force-renewal parameter
revocation will be done per certificate
You would need to insert it into Zimbra.
That's right, so I move the files to the new folder and redo the command under zimbra and see how it goes