Hi, my SSL suddenly (and without my interference) stopped working. It has been working fine for the past few months since I set it up. I’ve spent the day googling and trying to find a solution, but I’m not sure I even understand what the problem is (I haven’t done backend stuff for a very long time). I would appreciate any help.
I’ve checked that .well-known is chmod 755, and I tried creating a folder called acme-challenge (also 755) and adding a test file to it, but cannot access it through my browser. (file is “test” without any extension).
My domain is: stxclockapi.com
I ran this command: sudo certbot-auto renew --dry-run
It produced this output:
Saving debug log to /var/log/letsencrypt/letsencrypt.log
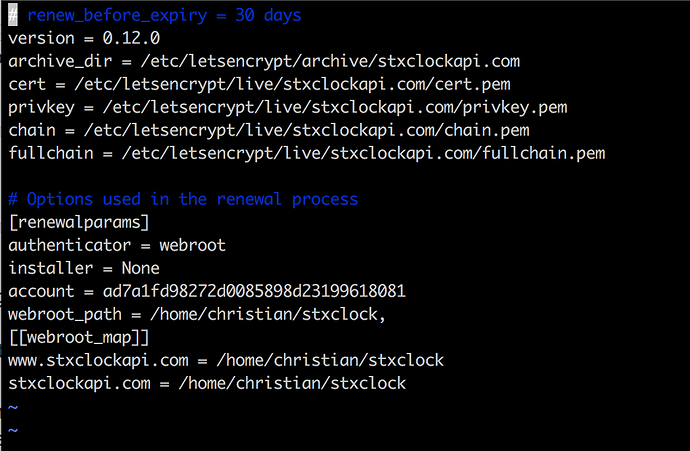
Processing /etc/letsencrypt/renewal/stxclockapi.com.conf
Cert is due for renewal, auto-renewing…
Renewing an existing certificate
Performing the following challenges:
http-01 challenge for stxclockapi.com
http-01 challenge for www.stxclockapi.com
Waiting for verification…
Cleaning up challenges
Attempting to renew cert (stxclockapi.com) from /etc/letsencrypt/renewal/stxclockapi.com.conf produced an unexpected error: Failed authorization procedure. stxclockapi.com (http-01): urn:acme:error:unauthorized :: The client lacks sufficient authorization :: Invalid response from http://stxclockapi.com/.well-known/acme-challenge/U2aNWhVfY6KPNnIAdM7m1-QTmtM2LvQO3MA9e_zsh9g: "
404 Not Found
", www.stxclockapi.com (http-01): urn:acme:error:unauthorized :: The client lacks sufficient authorization :: Invalid response from http://www.stxclockapi.com/.well-known/acme-challenge/V7BYJKbLlq4Di5wCYaeM5E98jevyLU8blH3zpgmlF30: " 404 Not Found
404 Not Found
". Skipping. ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates below have not been saved.)
All renewal attempts failed. The following certs could not be renewed:
/etc/letsencrypt/live/stxclockapi.com/fullchain.pem (failure)
** DRY RUN: simulating ‘certbot renew’ close to cert expiry
** (The test certificates above have not been saved.)
1 renew failure(s), 0 parse failure(s)
IMPORTANT NOTES:
-
The following errors were reported by the server:
Domain: stxclockapi.com
404 Not Found
Type: unauthorized
Detail: Invalid response from
http://stxclockapi.com/.well-known/acme-challenge/U2aNWhVfY6KPNnIAdM7m1-QTmtM2LvQO3MA9e_zsh9g:
"404 Not Found
"Domain: www.stxclockapi.com
404 Not Found
Type: unauthorized
Detail: Invalid response from
http://www.stxclockapi.com/.well-known/acme-challenge/V7BYJKbLlq4Di5wCYaeM5E98jevyLU8blH3zpgmlF30:
"404 Not Found
"To fix these errors, please make sure that your domain name was
entered correctly and the DNS A/AAAA record(s) for that domain
contain(s) the right IP address.
My web server is (include version): Nginx 1.4.6
The operating system my web server runs on is (include version): Ubuntu 14.04.5
My hosting provider, if applicable, is: Digital Ocean for the server, goDaddy for the domain
I can login to a root shell on my machine (yes or no, or I don’t know): yes
I’m using a control panel to manage my site (no, or provide the name and version of the control panel): no
This is my “sites-enabled”: