Complete Challenges with Certbot
We are going to use the manual plugin with DNS challenges and CSRs we created above
I am using a virtual environment (Certbot-Production for this)
Note: you should use --staging flag for learning and practice. Once you can issue certificates reliably from the staging authority and remove --staging and obtain production certificates.
CSR for jks-simple-cert.firecube.xyz
Command:
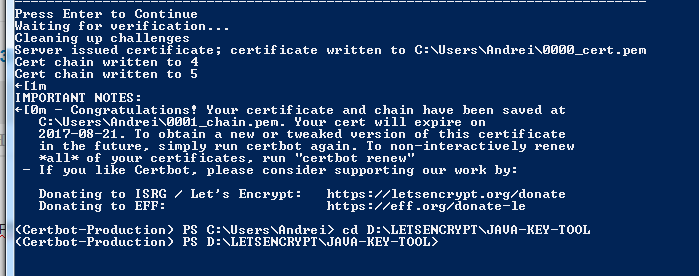
certbot certonly --manual --csr D:\LETSENCRYPT\JAVA-KEY-TOOL\jks-simple-cert_firecube_xyz.csr --preferred-challenges "dns"
CSR for jks-simple-cert.firecube.xyz
Command:
certbot certonly --manual --csr D:\LETSENCRYPT\JAVA-KEY-TOOL\jks-san-cert_firecube_xyz.csr --preferred-challenges "dns"
I renamed the certs along the lines of what they are (certs only and certs with intermediates)