My domain is: drupal9test.sinet.ca
I ran this command: N/A
It produced this output :N/A
My web server is (include version): Apache 2.4.54
The operating system my web server runs on is (include version): 5.4.0-163-generic #180-Ubuntu
My hosting provider, if applicable, is: pair.com
I can login to a root shell on my machine (yes or no, or I don't know): no
I'm using a control panel to manage my site (no, or provide the name and version of the control panel): pair.com admin
The version of my client is (e.g. output of certbot --version or certbot-auto --version if you're using Certbot): N/A
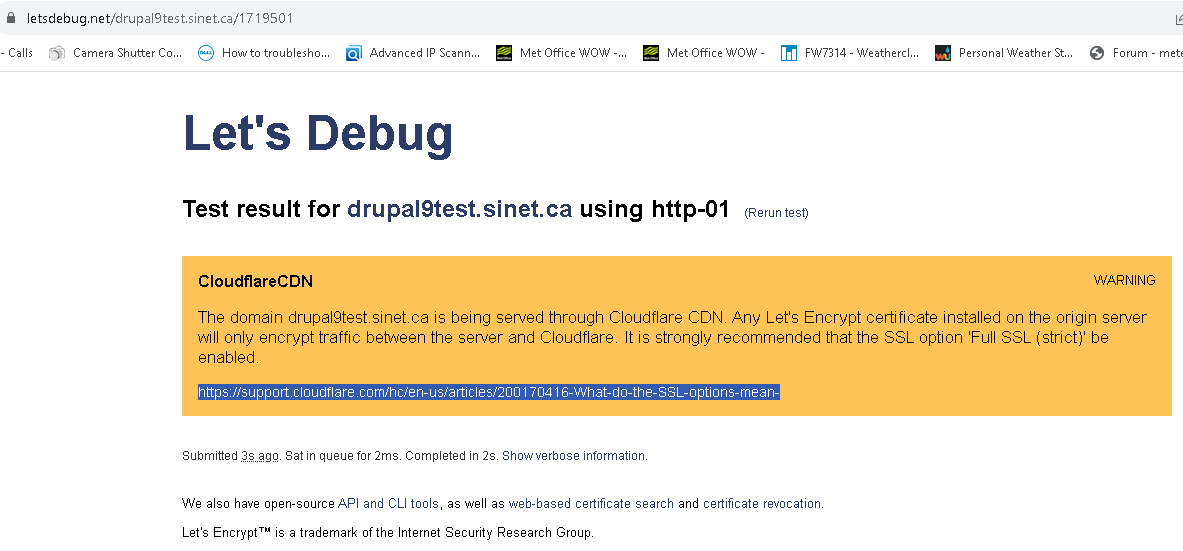
I have a number of shared hosting servers. My service provider supports Let's Encrypt certificates through their admin platform. When requesting a certificate, I disable the default of adding the www. to the subdomain. Once the certificate has been issued and loaded, my service provider automatically re-directs http:// requests to https://. At this point, I enable Cloudflare proxy for my subdomain using the Full Strict option. Cloudflare also redirects http:// to https://. Everything works as expected
However, it appears that Let's Encrypt is unable to refresh the SSL certificate. About 23 days before it expires, I see daily attempts that originate from Cloudflare proxy servers:
162.158.245.78 - - [29/Nov/2023:18:07:32 -0700] "GET /.well-known/acme-challenge HTTP/1.1" 301 627 "-" "Mozilla/5.0 (compatible; Let's Encrypt validation server; +https://www.letsencrypt.org)"
162.158.245.78 - - [29/Nov/2023:18:07:32 -0700] "GET /.well-known/acme-challenge/ HTTP/1.1" 200 5642 "http://drupal9test.sinet.ca/.well-known/acme-challenge/ "Mozilla/5.0 (compatible; Let's Encrypt validation server; +https://www.letsencrypt.org)"
If I disabled Cloudflare proxy, the certificate renewal completes successfully. The log shows the same commands, expect I see three pairs of requests (301 and 200) from three IPs, one registered to Internet Security Research Group, the other two to Amazon.
I asked pair.com and was told that:
Cloudflare will not validate when a domain name doesn't use the pair.com IP
address. Our implementation of Cloudflare is built in such a way that it
only uses http/https validation. When the public-facing IP address is
Cloudflare Let's Encrypt will not renew nor successfully install as a new
cert.
Is this a limitation of pair.com's implementation or a feature of Let's Encrypt? I had been successfully renewing Let's Encrypt certificates on an Amazon EC2 instance behind Cloudflare as recently as March 2022 https://forum.virtualmin.com/t/lets-encrypt-renewal-failing-during-secondary-validation-invalid-response-aws-behind-cloudflare/114247. At the time, it seemed to be an issue with Cloudflare switching their proxy servers to IPV6 while my Amazon server was still on IPV4. The recommendation was to use certbot but I could not find a version that supported my rather old Linux version.