But I'm talking about the error message that you sent me yesterday
" acme: error code 403 "urn:ietf:params:acme:error:unauthorized": 2a02:8429:d44b:ea01:d9cc:3f4:1d97:810d: Invalid response from https://dev.cogetep.fr/.well-known/acme-challenge/zlD9v3krK9AbhgUhWe0hsiecDM9gwscIcpd6caiyr7s : 404"
and with which I don't know what to do. So, I thought it was good, obviously wrongly, to start looking for suspicious points in the server which could be the cause of this error message. What exactly do you recommend I do?
The "404" error from Let's Debug is expected. What was important about that was showing your redirect to HTTPS and the use of IPv6
What is the error you get when actually requesting a cert?
The ACME client is Certbot version 2.11.0. My problem is not obtaining the certificate :

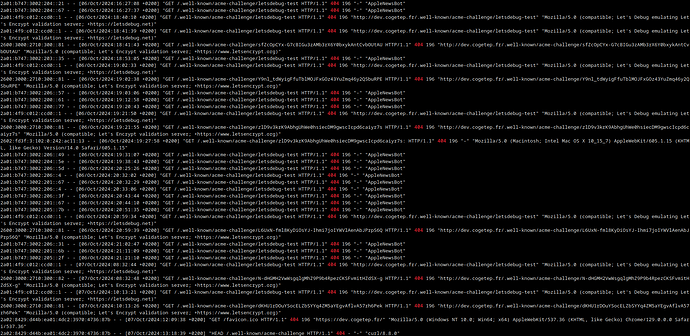
The problem is the failure of the ACME challenge (extract from access_log below).
Why is that a problem? It's normal for challenges that do not exist (due to the testing nature of the challenges you've shown) to return a 404 file not found.
It's only a problem if you're actually having issues with obtaining or renewing your certificate.
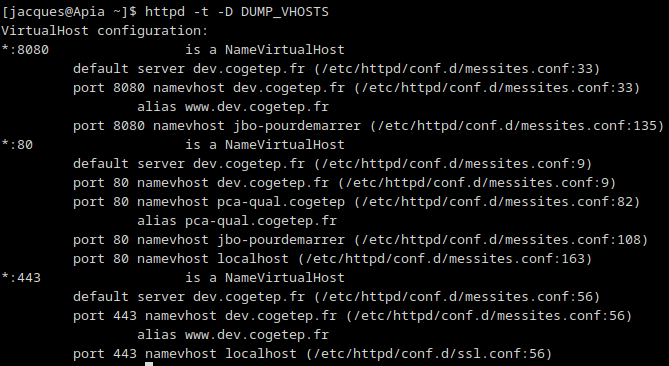
What shows?:
sudo apachectl -t -D DUMP_VHOSTS
Hello OSIRIS.
I have a problem understanding the fund. Can you please precise "due to the testing nature of the challenges I've shown".
Often requests for challenges will get to your webserver which are NOT from Let's Encrypt. For example, Google bot will recognise the challenge URL from e.g. this thread and will try to get it. But in the mean time, that challenge is already gone, because it's not used by Let's Encrypt any longer. So your webserver will reply with an expected 404 file not found.
Only if Let's Encrypt requests a challenge when you're obtaining or renewing a certificate, THEN are the challenge requests in your log important. The others you can ignore.
Thank you OSIRIS for these enlightening details.
So I have to understand that there is no Let's Encrypt problem. That the error message returned by Let's Debug is linked to the fact that the domain dev.cogetep.fr is inaccessible in IP v4 from the internet (I will check this point with my internet operator).
And regarding the presence of the error message “AH01909: localhost:443:0 server certificate does NOT include an ID which matches the server name” in the ssl_error_log file (http server), do you recommend that I open another topic ?
You can test the Certbot renewal with this. It will not affect your existing production certs. It is only a test
sudo certbot renew --dry-run
If that is successful you should not have any problem getting certs
That is an Apache warning message. It is not related to Let's Encrypt. You should review your VirtualHost in the /etc/httpd/conf.d/ssl.conf file.
If you do not understand the error please show that file
Result is OK

I don't understand the error, here is ssl.conf file
#
# When we also provide SSL we have to listen to the
# standard HTTPS port in addition.
#
Listen 443 https
##
## SSL Global Context
##
## All SSL configuration in this context applies both to
## the main server and all SSL-enabled virtual hosts.
##
# Pass Phrase Dialog:
# Configure the pass phrase gathering process.
# The filtering dialog program (`builtin' is a internal
# terminal dialog) has to provide the pass phrase on stdout.
SSLPassPhraseDialog exec:/usr/libexec/httpd-ssl-pass-dialog
# Inter-Process Session Cache:
# Configure the SSL Session Cache: First the mechanism
# to use and second the expiring timeout (in seconds).
SSLSessionCache shmcb:/run/httpd/sslcache(512000)
SSLSessionCacheTimeout 300
# Pseudo Random Number Generator (PRNG):
# Configure one or more sources to seed the PRNG of the
# SSL library. The seed data should be of good random quality.
# WARNING! On some platforms /dev/random blocks if not enough entropy
# is available. This means you then cannot use the /dev/random device
# because it would lead to very long connection times (as long as
# it requires to make more entropy available). But usually those
# platforms additionally provide a /dev/urandom device which doesn't
# block. So, if available, use this one instead. Read the mod_ssl User
# Manual for more details.
SSLRandomSeed startup file:/dev/urandom 256
SSLRandomSeed connect builtin
#SSLRandomSeed startup file:/dev/random 512
#SSLRandomSeed connect file:/dev/random 512
#SSLRandomSeed connect file:/dev/urandom 512
#
# Use "SSLCryptoDevice" to enable any supported hardware
# accelerators. Use "openssl engine -v" to list supported
# engine names. NOTE: If you enable an accelerator and the
# server does not start, consult the error logs and ensure
# your accelerator is functioning properly.
#
SSLCryptoDevice builtin
#SSLCryptoDevice ubsec
##
## SSL Virtual Host Context
##
<VirtualHost _default_:443>
# General setup for the virtual host, inherited from global configuration
#DocumentRoot "/var/www/html"
#ServerName www.example.com:443
# Use separate log files for the SSL virtual host; note that LogLevel
# is not inherited from httpd.conf.
ErrorLog logs/ssl_error_log
TransferLog logs/ssl_access_log
LogLevel warn
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# List the protocol versions which clients are allowed to connect with.
# The OpenSSL system profile is configured by default. See
# update-crypto-policies(8) for more details.
#SSLProtocol all -SSLv3
#SSLProxyProtocol all -SSLv3
# User agents such as web browsers are not configured for the user's
# own preference of either security or performance, therefore this
# must be the prerogative of the web server administrator who manages
# cpu load versus confidentiality, so enforce the server's cipher order.
SSLHonorCipherOrder on
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
# The OpenSSL system profile is configured by default. See
# update-crypto-policies(8) for more details.
SSLCipherSuite PROFILE=SYSTEM
SSLProxyCipherSuite PROFILE=SYSTEM
# Point SSLCertificateFile at a PEM encoded certificate. If
# the certificate is encrypted, then you will be prompted for a
# pass phrase. Note that restarting httpd will prompt again. Keep
# in mind that if you have both an RSA and a DSA certificate you
# can configure both in parallel (to also allow the use of DSA
# ciphers, etc.)
# Some ECC cipher suites (http://www.ietf.org/rfc/rfc4492.txt)
# require an ECC certificate which can also be configured in
# parallel.
SSLCertificateFile /etc/pki/tls/certs/localhost.crt
# Server Private Key:
# If the key is not combined with the certificate, use this
# directive to point at the key file. Keep in mind that if
# you've both a RSA and a DSA private key you can configure
# both in parallel (to also allow the use of DSA ciphers, etc.)
# ECC keys, when in use, can also be configured in parallel
SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convenience.
#SSLCertificateChainFile /etc/pki/tls/certs/server-chain.crt
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
#SSLCACertificateFile /etc/pki/tls/certs/ca-bundle.crt
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# Access Control:
# With SSLRequire you can do per-directory access control based
# on arbitrary complex boolean expressions containing server
# variable checks and other lookup directives. The syntax is a
# mixture between C and Perl. See the mod_ssl documentation
# for more details.
#<Location />
#SSLRequire ( %{SSL_CIPHER} !~ m/^(EXP|NULL)/ \
# and %{SSL_CLIENT_S_DN_O} eq "Snake Oil, Ltd." \
# and %{SSL_CLIENT_S_DN_OU} in {"Staff", "CA", "Dev"} \
# and %{TIME_WDAY} >= 1 and %{TIME_WDAY} <= 5 \
# and %{TIME_HOUR} >= 8 and %{TIME_HOUR} <= 20 ) \
# or %{REMOTE_ADDR} =~ m/^192\.76\.162\.[0-9]+$/
#</Location>
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o StrictRequire:
# This denies access when "SSLRequireSSL" or "SSLRequire" applied even
# under a "Satisfy any" situation, i.e. when it applies access is denied
# and no other module can change it.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory "/var/www/cgi-bin">
SSLOptions +StdEnvVars
</Directory>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is sent or allowed to be received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is sent and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
BrowserMatch "MSIE [2-5]" \
nokeepalive ssl-unclean-shutdown \
downgrade-1.0 force-response-1.0
# Per-Server Logging:
# The home of a custom SSL log file. Use this when you want a
# compact non-error SSL logfile on a virtual host basis.
CustomLog logs/ssl_request_log \
"%t %h %{SSL_PROTOCOL}x %{SSL_CIPHER}x \"%r\" %b"
</VirtualHost>
That warning message is for the above VirtualHost. The Apache ServerName does not match what you used for the name inside that localhost.crt file.
The ServerName is commented out so Apache chooses a name and in your case it is localhost
People trying to connect to your localhost (or default) with HTTPS will fail because of mis-matched names. But, why is that a problem? If you are connecting to your own localhost you can use HTTP (not HTTPS). Normal requests to your domain will be handled by your other VirtualHost with your Let's Encrypt cert.
In any case, this is general Apache setup options. Not specific for Let's Encrypt. I think it is fine to just ignore that warning.
It's clearer to me. Thank you MikeMcQ
What shows?:
![]()
what is wrong with this line?
In order to tell you what may be wrong...
We first need to see that file.
Here is the file messites.conf
#Mise en écoute du serveur sur le port 8080
#Listen 8080
# Serveur virtuel qui héberge le site "dev.cogetep.fr/"
# Le serveur écoute et accepte les connexions sur le port 80 pour toutes les adresses IPv4 et toutes les adresses IPv6
<VirtualHost *:80 [::]:80>
# home du site : URL = http://dev.cogetep.fr/
ServerName dev.cogetep.fr
#ServerAlias www.dev.cogetep.fr
# Dossier racine du site (ce dossier contient notamment le fichier index.html qui décrit la page d'accueil du site)
#DocumentRoot "/var/www/dev.cogetep
#DocumentRoot "/var/www/dev.cogetep/target/StageIntercoSageClient-1.0"
DocumentRoot "/home/jacques/glassfish6/glassfish/domains/domain1/applications"
#DocumentRoot "/home"
<Directory "/home/jacques/glassfish6/glassfish/domains/domain1/applications">
# Autoriser l'accès au répertoire
Require all granted
#Options Indexes FollowSymLinks
</Directory>
RewriteEngine on
RewriteCond %{SERVER_NAME} =www.dev.cogetep.fr [OR]
RewriteCond %{SERVER_NAME} =dev.cogetep.fr
RewriteRule ^ https://%{SERVER_NAME}%{REQUEST_URI} [END,NE,R=permanent]
</VirtualHost>
<VirtualHost *:8080 [::]:8080>
# home du site : URL = http://dev.cogetep.fr/
ServerName dev.cogetep.fr
ServerAlias www.dev.cogetep.fr
# Dossier racine du site (ce dossier contient notamment le fichier index.html qui décrit la page d'accueil du site)
DocumentRoot "/home/jacques/glassfish6/glassfish/domains/domain1/applications"
<Directory "/home/jacques/glassfish6/glassfish/domains/domain1/applications">
# Autoriser l'accès au répertoire
Require all granted
#Options Indexes FollowSymLinks
</Directory>
RewriteEngine on
RewriteCond %{SERVER_NAME} =www.dev.cogetep.fr [OR]
RewriteCond %{SERVER_NAME} =dev.cogetep.fr
RewriteRule ^ https://%{SERVER_NAME}%{REQUEST_URI} [END,NE,R=permanent]
</VirtualHost>
# Serveur virtuel qui héberge le site "dev.cogetep.fr/"
# Le serveur écoute et accepte les connexions sur le port 443 (https) pour toutes les adresses IPv4 et toutes les adresses IPv6
<VirtualHost *:443 [::]:443>
# home du site : URL = https://dev.cogetep.fr/
ServerName dev.cogetep.fr
ServerAlias www.dev.cogetep.fr
# Dossier racine du site (ce dossier contient notamment le fichier index.html qui décrit la page d'accueil du site)
#DocumentRoot "/var/www/dev.cogetep
#DocumentRoot "/var/www/dev.cogetep/target/StageIntercoSageClient-1.0"
DocumentRoot "/home/jacques/glassfish6/glassfish/domains/domain1/applications"
#DocumentRoot "/home"
<Directory "/home/jacques/glassfish6/glassfish/domains/domain1/applications">
# Autoriser l'accès au répertoire
Require all granted
#Options Indexes FollowSymLinks
</Directory>
Include /etc/letsencrypt/options-ssl-apache.conf
SSLCertificateFile /etc/letsencrypt/live/dev.cogetep.fr/fullchain.pem
SSLCertificateKeyFile /etc/letsencrypt/live/dev.cogetep.fr/privkey.pem
</VirtualHost>
# Serveur virtuel qui héberge le site "pca-qual.cogetep.fr"
# Le serveur écoute et accepte les connexions sur le port 80 pour toutes les adresses IPv4 et toutes les adresses IPv6
<VirtualHost *:80 [::]:80>
# home du site : URL = http://pca-qual.cogetep.fr/
ServerName pca-qual.cogetep
ServerAlias pca-qual.cogetep.fr
#ServerAlias www.pca-qual.cogetep.fr
# Dossier racine du site (ce dossier contient notamment le fichier index.html qui décrit la page d'accueil du site)
DocumentRoot "/var/www/dev.cogetep"
#DocumentRoot "/var/www/dev.cogetep/target/StageIntercoSageClient-1.0"
#DocumentRoot "/home/jacques/NetBeansProjects/StageIntercoSageClient/target/StageIntercoSageClient-1.0"
#DocumentRoot "/home"
<Directory "/home/jacques/NetBeansProjects/StageIntercoSageClient/target/StageIntercoSageClient-1.0">
# Autoriser l'accès au répertoire
Require all granted
#Options Indexes FollowSymLinks
</Directory>
# Retourner l'erreur n°404 chaque fois que l'url demandé ne correspond à aucun fichier
<Location "/">
#try_files $uri $uri/ =404
</Location>
</VirtualHost>
<VirtualHost *:80 [::]:80>
# home du site : URL = http://jbo-pourdemarrer.fr/
ServerName jbo-pourdemarrer
#ServerAlias jbo-pourdemarrer.fr www.jbo-pourdemarrer.fr
# Dossier contenant les pages
#DocumentRoot /var/www/jbo-pourdemarrer
DocumentRoot /home/jacques/glassfish6/glassfish/domains/domain1/applications
<Directory /home/jacques/glassfish6/glassfish/domains/domain1/applications>
# Autoriser l'accès au répertoire
Require all granted
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
AllowOverride FileInfo AuthConfig Limit
</Directory>
<Directory /var/www/jbo-pourdemarrer>
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
AllowOverride FileInfo AuthConfig Limit
</Directory>
# jeu de caractères (UTF-8 par défaut)
AddDefaultCharset ISO-8859-1
</VirtualHost>
<VirtualHost *:8080 [::]:8080>
# home du site : URL = http://jbo-pourdemarrer.fr/
ServerName jbo-pourdemarrer
#ServerAlias jbo-pourdemarrer.fr www.jbo-pourdemarrer.fr
# Dossier contenant les pages
#DocumentRoot /var/www/jbo-pourdemarrer
DocumentRoot /home/jacques/glassfish6/glassfish/domains/domain1/applications
<Directory /home/jacques/glassfish6/glassfish/domains/domain1/applications>
# Autoriser l'accès au répertoire
Require all granted
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
AllowOverride FileInfo AuthConfig Limit
</Directory>
<Directory /var/www/jbo-pourdemarrer>
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
AllowOverride FileInfo AuthConfig Limit
</Directory>
# jeu de caractères (UTF-8 par défaut)
AddDefaultCharset ISO-8859-1
</VirtualHost>
# Hôte virtuel par défaut
<VirtualHost *:80 [::]:80>
# home du site : URL = http://localhost
ServerName localhost
# Dossier contenant les pages
DocumentRoot "/var/www/html
# Activation des sites de quelques utilisateurs : http://localhost/jack
UserDir enabled jack
UserDir public_html
<Directory /home/*/public_html>
AllowOverride all
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
</Directory>
# Activation de l'adresse : http://localhost/server-status
<Location /server-status>
SetHandler server-status
Require ip 127.0.0.1
Require ip ::1
</Location>
# Activation de l'adresse : http://localhost/server-info
<Location /server-info>
SetHandler server-info
Require ip 127.0.0.1
Require ip ::1
</Location>
</VirtualHost>
@rg305 what problem are you chasing? --dry-run now working see