JoyalV
March 4, 2017, 6:03am
1
So I have a cron job for renewing the letsencrypt certificate, I was wondering if I need to add an HSTS flag (if so, how)? Or will it automatically do it on renewal?
30 2 * * 1 /usr/bin/letsencrypt renew >> var/log/le-renew.log
Server: Ubuntu 16.04 Xenial
jsha
March 4, 2017, 7:39am
2
If you provided the HSTS flag at issuance / installation time, there is no need to specify it for renewal.
JoyalV
March 4, 2017, 3:34pm
3
Thank you.
Also if I setup with HSTS, does it stop redirecting to HTTPS? I can still seem to access site with HTTP
schoen
March 4, 2017, 6:11pm
4
Those are separate issues. HSTS tells browsers (that have already accessed the site in HTTPS) to go to the HTTPS version automatically in the future. The redirection tells browsers (that are currently visiting the site in HTTP) to go to the HTTPS version right now. They can exist independently, and ideally you should use both.
JoyalV
March 5, 2017, 2:29am
5
Well in Certbot I selected secure so everything redirects but if I use www. It doesn’t seem to redirect.
JoyalV
March 10, 2017, 5:30am
6
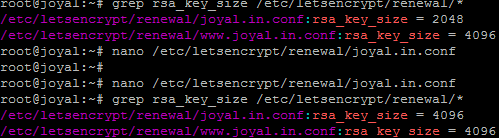
Does this also apply for the rsa-key-size flag?
Yes. You can confirm it with something like "grep rsa_key_size /etc/letsencrypt/renewal/*".
JoyalV
March 10, 2017, 5:40am
8
It seemed to have only done it for the ServerAlias; www.domain.com instead of domain.com
Do you know why it might be?
I’m sorry, but i’m not very familiar with the Certbot Apache plugin.
If you paste your Apache configuration – preferably without redacting anything – someone else may be able to help.
Ohhh, that’s what you meant. I misunderstood you.
I don’t know the answer to this , either. My best guess is that you forgot to specify --rsa-key-size when issuing one of the certificates.
JoyalV
March 10, 2017, 5:47am
12
Well what also bothers me it that, it is only updating the certs for www also when I try re-installing
At the moment, public records – which may be about 2 hours old – show that you most recently issued several certificates on March 4 and March 5, all of them 2048 bits.
https://crt.sh/?q=%joyal.in
One of them covers only joyal.in; the other 3 cover both joyal.in and www.joyal.in.
It’s possible that your recent commands only replaced one of the certificates. (Probably the one that covers both names.)
These commands might be interesting:
openssl x509 -in /etc/letsencrypt/live/joyal.in/cert.pem -noout -text | egrep 'Before|DNS|Public-Key'
openssl x509 -in /etc/letsencrypt/live/www.joyal.in/cert.pem -noout -text | egrep 'Before|DNS|Public-Key'
Indeed, you probably don’t need to have two separate certificates…
Edit:
Also, what letsencrypt commands did you run recently?
Edit:
One 4096-bit certificate covering both names was issued an hour or two ago. (04:28 UTC.)
JoyalV
March 10, 2017, 6:23am
14
I did the letsencrypt Apache one.
SSL labs was showing 4096
system
April 9, 2017, 6:23am
15
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.