Please fill out the fields below so we can help you better. Note: you must provide your domain name to get help. Domain names for issued certificates are all made public in Certificate Transparency logs (e.g. https://crt.sh/?q=example.com), so withholding your domain name here does not increase secrecy, but only makes it harder for us to provide help.
My domain is:
sandbox.aberela.tk
I ran this command:
certbot renew --dry-run
It produced this output:
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Processing /etc/letsencrypt/renewal/sandbox.aberela.tk.conf
Cert not due for renewal, but simulating renewal for dry run
Plugins selected: Authenticator dns-google, Installer None
Starting new HTTPS connection (1): acme-staging-v02.api.letsencrypt.org
Renewing an existing certificate
Performing the following challenges:
dns-01 challenge for sandbox.aberela.tk
URL being requested: GET https://www.googleapis.com/discovery/v1/apis/dns/v1/rest
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones?alt=json&dnsName=sandbox.aberela.tk.
Attempting refresh to obtain initial access_token
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones?alt=json&dnsName=aberela.tk.
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones/1722142954094966035/rrsets?alt=json
URL being requested: POST https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones/1722142954094966035/changes?alt=json
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones/1722142954094966035/changes/155?alt=json
Waiting 60 seconds for DNS changes to propagate
Waiting for verification…
Cleaning up challenges
URL being requested: GET https://www.googleapis.com/discovery/v1/apis/dns/v1/rest
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones?alt=json&dnsName=sandbox.aberela.tk.
Attempting refresh to obtain initial access_token
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones?alt=json&dnsName=aberela.tk.
URL being requested: GET https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones/1722142954094966035/rrsets?alt=json
URL being requested: POST https://www.googleapis.com/dns/v1/projects/managed-dns/managedZones/1722142954094966035/changes?alt=json
new certificate deployed without reload, fullchain is
/etc/letsencrypt/live/sandbox.aberela.tk/fullchain.pem
** DRY RUN: simulating ‘certbot renew’ close to cert expiry
** (The test certificates below have not been saved.)
My web server is (include version):
I am using dns authentication.
The operating system my web server runs on is (include version):
I am using dns authentication.
My hosting provider, if applicable, is:
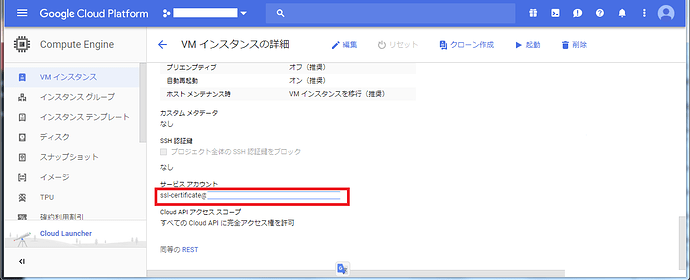
Google Cloud Platform, GCE
I can login to a root shell on my machine (yes or no, or I don’t know):
yes
I’m using a control panel to manage my site (no, or provide the name and version of the control panel):
no