Please fill out the fields below so we can help you better. Note: you must provide your domain name to get help. Domain names for issued certificates are all made public in Certificate Transparency logs (e.g. crt.sh | example.com ), so withholding your domain name here does not increase secrecy, but only makes it harder for us to provide help.
My domain is: incursionofficial.xyz
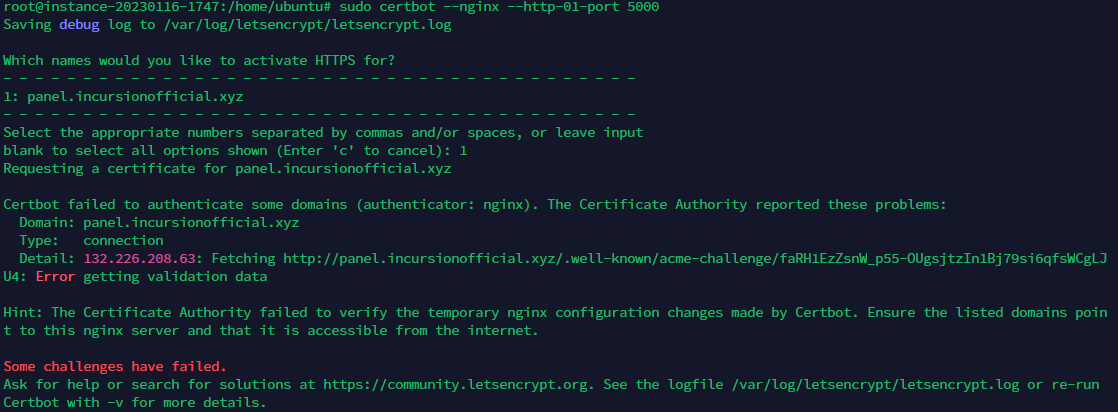
I ran this command: sudo certbot --nginx --http-01-port 5000
It produced this output:
My web server is (include version): Idk what this means
The operating system my web server runs on is (include version): Canonical-Ubuntu-22.04-aarch64-2022.11.06-0
My hosting provider, if applicable, is: Oracle Cloud Free Tier
I can login to a root shell on my machine (yes or no, or I don't know): Yes
I'm using a control panel to manage my site (no, or provide the name and version of the control panel): Oracle Control Panel (I think)
The version of my client is (e.g. output of certbot --version or certbot-auto --version if you're using Certbot): certbot 1.21.0
Im not that good at this stuff so any help would be great
_az
January 18, 2023, 8:31pm
2
What led you to use --http-01-port 5000?
For this to work, your website needs to be functioning and accessible at http://panel.incursionofficial.xyz . Currently it isn't.
3 Likes
I was looking things up seeing what might work so i tried that but it is the same message as i got when i first tried to set it up.
Im trying to setup pterodactyl and the server is up which is what the domain is listed to and the ip and domain have been pointed if that is what you mean.
rg305
January 18, 2023, 8:45pm
5
Is your server behind CloudFlare CDN?
Also:
You shouldn't be "trying" things on the production environment.--dry-run
2 Likes
rg305:
--dry-run
yes my domain is pointed through cloudflare
I believe i need a https cert
rg305
January 18, 2023, 8:47pm
9
CloudFlare can easily provide one - that works with their CDN.
2 Likes
May I ask how i would do that?
rg305
January 18, 2023, 8:48pm
11
Yes, you should.
2 Likes
Ok thank you i will ask now and i shall respond back to see if it works or not.
Thank you for your help
1 Like
_az
January 18, 2023, 9:17pm
13
It isn't, the domain is using Cloudflare DNS but it's not using the CDN.
I don't think that going down the route of a Cloudflare Universal SSL certificate is what OP was looking for.
it seems like things are working now compared to first time I tried to connect.
Can you try this now:
certbot certonly -d panel.incursionofficial.xyz --nginx --dry-run
3 Likes
rg305
January 18, 2023, 11:55pm
14
How does one explain this?
curl -Ii http://panel.incursionofficial.xyz/
HTTP/1.1 523
Date: Wed, 18 Jan 2023 20:42:23 GMT
Content-Length: 0
Connection: keep-alive
Cache-Control: no-store, no-cache
CF-Cache-Status: DYNAMIC
Report-To: {"endpoints":[{"url":"https:\/\/a.nel.cloudflare.com\/report\/v3?s=Uf3Wk8LOLE1M0HgvRUVfeg7ohB094qvHnWarCemYstv4qvlbIiqvagj0xKD3spayJ2nxO1o7jJONO4f2GY0xKyPGCTGIMPcEKEtLVuJYeB7cRgTa7O23yX7%2B0OMkDoAnTV3qzYq%2BUOlrqDJQ%2FlH2BRTxlRCAmZddWD4%3D"}],"group":"cf-nel","max_age":604800}
NEL: {"success_fraction":0,"report_to":"cf-nel","max_age":604800}
Server: cloudflare
CF-RAY: 78ba282abd312251-MIA
alt-svc: h3=":443"; ma=86400, h3-29=":443"; ma=86400
2 Likes
Supplemental information
$ nmap panel.incursionofficial.xyz
Starting Nmap 7.91 ( https://nmap.org ) at 2023-01-18 16:07 PST
Nmap scan report for panel.incursionofficial.xyz (132.226.208.63)
Host is up (0.16s latency).
Not shown: 995 filtered ports
PORT STATE SERVICE
22/tcp open ssh
53/tcp closed domain
80/tcp open http
443/tcp closed https
5000/tcp closed upnp
Nmap done: 1 IP address (1 host up) scanned in 10.46 seconds
$ curl -Ii http://panel.incursionofficial.xyz
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
Cache-Control: no-cache, private
Date: Thu, 19 Jan 2023 00:14:15 GMT
Set-Cookie: XSRF-TOKEN=eyJpdiI6InNkdTN3V1NoWnkrNmJjRVVrenQ5ZWc9PSIsInZhbHVlIjoiRzBHYit4U3pxSG00SVp6S2JKY0gzRjNvUXExcTVtK012eUxFMFNVNytobTI4YlNiNUFzOEJpVVJXSHpkZjRyVGdjSEpOaklzN1Q2cDdLd0Rmdi8wRzBIYTdxOWZYOWFBOFhzTTRaaS84UlBHUFpXNHdEN08yMVBmZmlwTU5yUEciLCJtYWMiOiJhZTU5NzI3ODAyYjI4MmJmMTM4ZGZmOTMzYTAyM2NhMGRmMGEzODJiMmFmMGYzOTA0ZTI4OWZhZWRiMTRiM2VhIiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:14:15 GMT; Max-Age=43200; path=/; secure; samesite=lax
Set-Cookie: pterodactyl_session=eyJpdiI6ImpJRWhQUHAwSzNNazlpUFNTVmZPdVE9PSIsInZhbHVlIjoiaGMwY2tESGl0QU8vNDdGdmlEblFDWEhQUjBnTm5oOGJzVytISkRIdER3UFlQSHNyWUljMUYwT3V2NDRDZDYyNkNrRjRrRXVIdmQ2bldmSnZsQTdDZ1Y2MC9UbFNOcGxHczBxUDRDMDRlVk8xb3lLaDgwYVZLMHIrSUozTUxzc3oiLCJtYWMiOiJhMzdmZjkzNDYyZGQ4MWUyMjFhMTVjODExMDA3ZWM3YWExYjY2NThlOGRkYWRkOTE5OGQ4ODM2ZGMwMDZiYjg4IiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:14:15 GMT; Max-Age=43200; path=/; secure; httponly; samesite=lax
$ curl -Ii http://panel.incursionofficial.xyz -A "Mozilla/5.0 (compatible; Let's Encrypt validation server; +https://www.letsencrypt.org)"
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
Cache-Control: no-cache, private
Date: Thu, 19 Jan 2023 00:14:24 GMT
Set-Cookie: XSRF-TOKEN=eyJpdiI6Ik5Wc1RqempaaXdJT2RKY3NrVWVDb2c9PSIsInZhbHVlIjoiVVFVSlpPTTArZitteFBzMTNGUk9rdlNOVlJ3N0Q3T1VUc1FJcWVrdnllTDRHZlRTZWViOVlvc3U4aGZoTktDS2JaYjBzK1B5bmxiOXk0THU1MWZPTjd1cUZTbFZ0TTVNMlVmQnU1UHVEUGxRUUZodkRmZ1BNRzI4bU5PZGl4VU0iLCJtYWMiOiJkMTU3NGM5ZjkwMDNlYzJhZTk3ZDBiNTgwYjA2NjE2NjY1YTM4N2E2YzJlMTg5NWU2NGUzZThkNTk4MDFmNGEwIiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:14:24 GMT; Max-Age=43200; path=/; secure; samesite=lax
Set-Cookie: pterodactyl_session=eyJpdiI6IlpDa0VjM2N6cUp6WTE0KzVNSkhUdGc9PSIsInZhbHVlIjoiNHhiS0NkWXg5QnNnVC9xTlgrNFRtWU94c2VtL2pkQVBrczBHNS8xWTFiN1Z1aXVvRVM2MlQ4andicktKMitQanRJVmJmcTdWRHRqeUsxa3EzSzc1VHYrdkdJZEhxZ1hLS2VYRnNqRVowbzIycjdkZ1pTdTVDdGM0aEtZclRkVG4iLCJtYWMiOiJlZmE4MjRkMjhlNmJhZmM0YTVjNTI5MTI4MWE2OTdmMWZmYzhlM2RkMWM3NDYyYzUzM2ViM2RlZTM3ODhkNWM3IiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:14:24 GMT; Max-Age=43200; path=/; secure; httponly; samesite=lax
~$ curl -Ii http://panel.incursionofficial.xyz/.well-known/acme-challenge/sometestfile
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
Cache-Control: no-cache, private
Date: Thu, 19 Jan 2023 00:16:53 GMT
Set-Cookie: XSRF-TOKEN=eyJpdiI6Ik9xajR3UkhLcDdFY1Y2NklDMmNsM0E9PSIsInZhbHVlIjoic2VKQXRjS1plS3RVM3V2T1QrKzlZbko1Nko5dlFqcmk4Ylk5d2JtRWR6YjV6Y0dhVzExNi93NGt0RzJmaTh5SFQyZHhUUTkvZmMrWXN4K0szQ3R1WDFjaW54bEdXMnRPM21BcFRCK0ZvNm1CditlbGlnNW5GTUNCaEl2R0Rxa0EiLCJtYWMiOiJlY2JkODE3NzY1NTYzYTVkYjE2MmRiOGJiNWFkNWI4ZmFjZjI0Yzg5NDJmNDRiMzA3ZThmZGVmMmMwYjk3ZDYyIiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:16:53 GMT; Max-Age=43200; path=/; secure; samesite=lax
Set-Cookie: pterodactyl_session=eyJpdiI6Ik55ZC9pQk5iQWN4U0xZejU2ejU5VWc9PSIsInZhbHVlIjoiMUNnY3dMN3dFUWpNTEpDUzhmZjE5b1U3WVpXZjRyeGtBTWNydjFiNytBdnF1RDFwTEcvSzlEYTNiTlJBclFESUpXcFM4NHRDUkkvUit0WmgzRWZnek1qQ1ppbTRzaGNCb3hkSWR3eHV1YzBpMEdkS3kyMlA5a0NEYzZJTFZFN2QiLCJtYWMiOiJmZTg2ZTY2MTk3N2M5NWRiNWJkYTBlZjAzMDAzMzZjNzg5ODU5MTc5ZmRlOTZkMjFkOWFmMWVlMDQxZWIyYmYxIiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:16:53 GMT; Max-Age=43200; path=/; secure; httponly; samesite=lax
$ curl -Ii http://panel.incursionofficial.xyz/.well-known/acme-challenge/sometestfile -A "Mozilla/5.0 (compatible; Let's Encrypt validation server; +https://www.letsencrypt.org)"
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Content-Type: text/html; charset=UTF-8
Connection: keep-alive
Cache-Control: no-cache, private
Date: Thu, 19 Jan 2023 00:17:12 GMT
Set-Cookie: XSRF-TOKEN=eyJpdiI6IkxVaHcvWEl2QmYvN1Vpam8vNDNXalE9PSIsInZhbHVlIjoiTTVMSVkyRUUyTW5yRWV6RDJLQTZvVU11elBjYTBtNEtDUjQ3SENRMXlBZW92blVjTktrWHNLNXBMK2psenBrdWZMdWpVdC93M255NFJYd2hPcDBmaWRVd2tNdkNtSU95enh0ajkxWEh1KzVTMndyZ0R3ZlUwa2h2bmYxRVcwSFkiLCJtYWMiOiI3NWFiZGZkMmU2Mjk0YTU5NWM0NTQ4MGY3NDJjYjkxNzdiZTNlNjEwOGRmOTdmOGRhNjJlODVmN2Y1ZTQ3ZGI3IiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:17:12 GMT; Max-Age=43200; path=/; secure; samesite=lax
Set-Cookie: pterodactyl_session=eyJpdiI6IlVJTXFUa2hyS09teHJXdzJtYno4cnc9PSIsInZhbHVlIjoiWVlxSGJoWEcvc1pYeHloTzMxby9iVkRVVG5QLzkySE5ZNWVmTFFoWm41R0hWTDlmMCswc1JUNko0WkdNa3BmNTV6Y3IwdElRRUlGbkpidElwVVkyMnh4OFNzVjRCKzNTYi9rdEx0YzhTdzFVVkdKSkFVNy9JWW1ld0RDSStZd2IiLCJtYWMiOiJjNGYwYmJhMDlmN2ZhOTdlMmFlZTZiNzMwMjEzMDUxNjgxMGFkM2M3YWFhZGY2YzBiZWVkYTcyNjI4ZjI4YjZhIiwidGFnIjoiIn0%3D; expires=Thu, 19-Jan-2023 12:17:12 GMT; Max-Age=43200; path=/; secure; httponly; samesite=lax
1 Like
_az
January 19, 2023, 12:31am
16
Dunno, stale cache? According to Cloudflare nameservers it's the non-CDN nginx server shown by @Bruce5051 's post.
3 Likes
I dislike inconsistent results.
1 Like
rg305
January 19, 2023, 12:53am
18
_az:
stale cache?
DNS TTL.
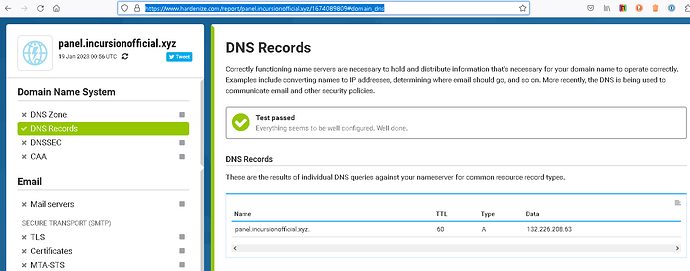
Then I had seen:
Name: panel.incursionofficial.xyz
Address: 104.21.50.203
Name: panel.incursionofficial.xyz
Address: 172.67.166.201
Name: panel.incursionofficial.xyz
Address: 2606:4700:3033::ac43:a6c9
Name: panel.incursionofficial.xyz
Address: 2606:4700:3033::6815:32cb
Now I see:
Name: panel.incursionofficial.xyz
Address: 132.226.208.63
[consistent with the IP shown in the error]
2 Likes
Something is going on with DNS for that domain
1 Like
MikeMcQ
January 19, 2023, 4:21am
20
@Incursion It looks like your nginx/Pterodactyl config is responding now on port 80 (http). Have you tried just with this now:
sudo certbot --nginx -d panel.incursionofficial.xyz --dry-run
If --dry-run (staging test) works then remove --dry-run to get and install a production cert.
If it fails, let us know the error.
It looks to me like you have nginx acting as a reverse proxy to Pterodactyl. That's fine. In this case nginx will need the cert to terminate HTTPS and then proxy to Pterodactyl.
So, the certbot --nginx plug-in will use the nginx port 80 server block to satisfy the cert challenge and then create an nginx server block for port 443 (https) based on the info in the port 80 server block.
curl -i panel.incursionofficial.xyz/
HTTP/1.1 200 OK
Server: nginx/1.18.0 (Ubuntu)
Set-Cookie: pterodactyl_session=eyJpdiI6IjZ1(...)
(other headers omitted)
(data - note title)
<!DOCTYPE html>
<html>
<head>
<title>Pterodactyl</title>
3 Likes
system
February 18, 2023, 4:22am
21
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.