Hi @rdill17
Your server is correctly configured. You can also use an online scanner to verify this. https://www.ssllabs.com/ssltest/analyze.html?d=dw.cameron.edu&hideResults=on&latest
So others can benefit below are some screenshots.
A) Download the Mozilla CA Root Cert bundle from here: https://curl.haxx.se/ca/cacert.pem
B) Place it in a folder (I have used a folder called LE_TRAINING)

C) run as you have
openssl s_client -connect dw.cameron.edu:443

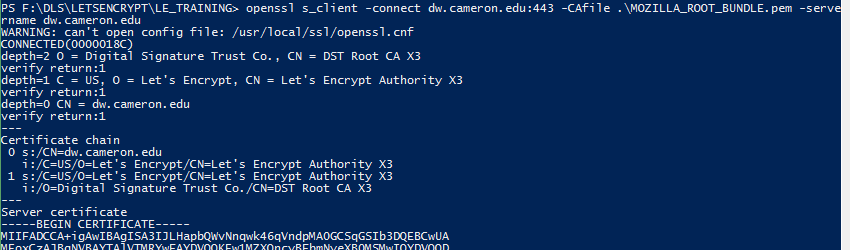
D) Run with the CA Root Cert Bundle
openssl s_client -connect dw.cameron.edu:443 -CAfile .\MOZILLA_ROOT_BUNDLE.pem
E) There is one other test I recommend you do with OpenSSL and that is to check SNI behaviour
openssl s_client -connect dw.cameron.edu:443 -CAfile .\MOZILLA_ROOT_BUNDLE.pem -servername dw.cameron.edu
Hope this helps. I would also suggest that you review Mozillas TLS Server Guidelines as you have some weak ciphers on your server.
https://mozilla.github.io/server-side-tls/ssl-config-generator/
Andrei